Are you concerned about the security of your Linux server? With the increasing number of cyber attacks, it’s crucial to take the necessary steps to protect your server from potential threats. In this informative blog post, we will discuss the essential measures you can take to secure your Linux server and keep it safe from malicious intruders. From implementing strong passwords and two-factor authentication to regularly updating your system and installing firewalls, we will cover all the key aspects of server security. By the end of this post, you will have a thorough understanding of how to effectively safeguard your Linux server from cyber attacks.
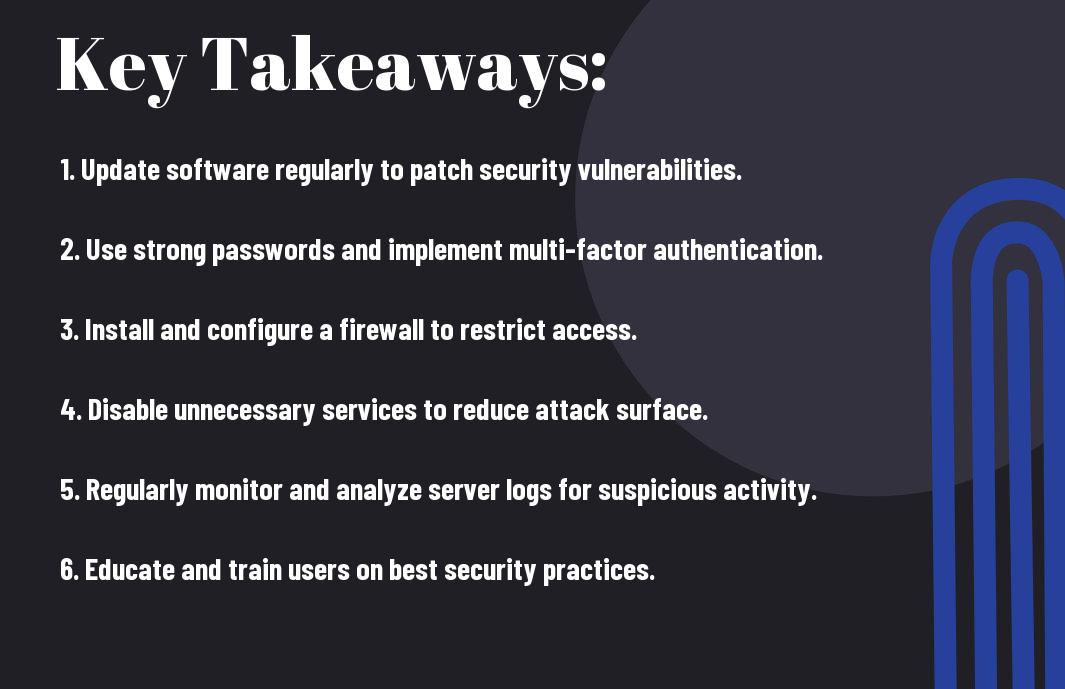
Key Takeaways:
- Update Regularly: Keeping your Linux server updated with the latest security patches and software updates is crucial for safeguarding it against potential cyber attacks.
- Implement Firewalls and Access Controls: Utilize firewalls and access control lists to restrict unauthorized access to your server, and consider implementing tools like SELinux for additional security measures.
- Regular Security Audits: Conducting regular security audits and vulnerability assessments can help identify potential weaknesses and take corrective measures to strengthen the server’s defenses against cyber attacks.
Establishing a Secure Foundation
Assuming you want to secure your Linux server from potential cyber attacks, it is crucial to establish a strong foundation from the start. This includes selecting the right Linux distribution for security and performing a minimal installation to reduce the attack surface.
Choosing the Right Linux Distribution for Security
When it comes to securing your Linux server, not all distributions are created equal. Some distributions are specifically designed with security in mind, offering built-in features and components to help protect your system. Look for a distribution that has a strong focus on security, such as Ubuntu Server, Fedora Security Lab, or OpenSUSE Leap. These distributions often come with advanced security tools and features, such as SELinux (Security-Enhanced Linux), AppArmor, and other security-focused components.
Performing a Minimal Installation
One of the most effective ways to secure your Linux server is to perform a minimal installation. By installing only the necessary components and packages, you can significantly reduce the attack surface and minimize the potential vulnerabilities on your system. When performing a minimal installation, you have greater control over what is installed on your server, reducing the risk of unnecessary services and applications that could be exploited by attackers. This approach allows you to build a lean and secure foundation for your server, providing a solid starting point for implementing additional security measures.
User and Authentication Security
To secure your Linux server from potential cyber attacks, it is essential to ensure user and authentication security. This involves managing user permissions and access controls, as well as implementing strong authentication mechanisms to prevent unauthorized access to your server.
Managing User Permissions and Access Controls
When it comes to user permissions and access controls, it is crucial to limit access to only those who require it for their specific role or task. Utilize role-based access control (RBAC) to assign permissions based on job responsibilities, ensuring that no user has more access privileges than necessary. Regularly review and update user permissions as roles and responsibilities change within your organization, and remove access for users who no longer require it.
Implementing Strong Authentication Mechanisms
Implementing strong authentication mechanisms is vital for securing your Linux server. Consider using two-factor authentication (2FA) to add an extra layer of security beyond just a password. You can also enforce password complexity requirements to ensure that user passwords are difficult to guess or crack. Furthermore, consider using SSH keys for secure access to your server, as they provide a more secure authentication method than traditional passwords.
Network Protection Strategies
For securing your Linux server from potential cyber attacks, it’s crucial to implement effective network protection strategies. This involves safeguarding your server from unauthorized access, data breaches, and other network-related threats.
Configuring Firewalls and Network Policies
One of the first steps in securing your Linux server is to configure firewalls and network policies. Firewalls act as a barrier between your server and potential threats by monitoring and controlling incoming and outgoing network traffic. You can set up firewall rules to only allow traffic from trusted sources and block any suspicious or unauthorized access attempts. Additionally, implementing network policies that dictate which devices have access to your server and what type of traffic is permitted can further strengthen your network security.
Monitoring and Auditing Network Traffic
Another essential aspect of network protection is monitoring and auditing the traffic that flows to and from your Linux server. By actively monitoring network traffic, you can identify and respond to any abnormal or suspicious behavior in real-time. This includes leveraging intrusion detection systems, network monitoring tools, and log analysis to keep an eye on potential security threats. Regularly auditing your network traffic allows you to track patterns, detect anomalies, and ensure compliance with security policies, ultimately enhancing the overall security of your server.
Maintaining System Security
Despite taking initial security measures, it’s important to continuously maintain the security of your Linux server to protect it from potential cyber attacks. This includes keeping the system and software up to date, conducting regular security audits, and vulnerability scanning.
Keeping the System and Software Up to Date
Regularly updating your Linux server’s operating system and software is crucial in ensuring its security. Software updates often include important security patches and bug fixes that protect your server from known vulnerabilities. By keeping your system up to date, you can mitigate potential risks and ensure that your server is equipped with the latest defenses against cyber threats.
Regular Security Audits and Vulnerability Scanning
Performing regular security audits and vulnerability scanning allows you to proactively identify and address any security weaknesses in your Linux server. By conducting routine assessments of your server’s security posture, you can identify and remediate potential vulnerabilities before they are exploited by attackers. Furthermore, vulnerability scanning tools can help you detect and prioritize security issues, allowing you to take the necessary actions to secure your server.
Advanced Security Measures
After implementing the basic security measures on your Linux server, you should consider implementing more advanced security measures to further strengthen your server’s defense against potential cyber attacks.
- Application Sandboxing and Isolation Techniques
- Intrusion Detection and Prevention Systems
Application Sandboxing and Isolation Techniques
When it comes to securing your Linux server, application sandboxing and isolation techniques play a crucial role in protecting your server from potential threats. Sandboxing involves running applications in a restricted environment, limiting their access to the rest of the system. By isolating applications, you can prevent the spread of malware and limit the potential damage caused by compromised applications. Popular tools such as Docker and LXC provide efficient sandboxing and isolation capabilities, allowing you to run applications in separate containers with restricted access to the underlying operating system.
Intrusion Detection and Prevention Systems
To bolster the security of your Linux server, implementing Intrusion Detection and Prevention Systems (IDPS) is vital. These systems continuously monitor your server for abnormal network activity and potential security breaches. With the ability to detect and respond to security threats in real-time, IDPS can significantly reduce the risk of unauthorized access, malware infections, and other cyber attacks. Tools like Snort and Suricata are widely used for network intrusion detection, while fail2ban provides effective protection against brute force attacks by blocking malicious IPs.
Securing Your Linux Server from Potential Cyber Attacks
Drawing together all the information and strategies discussed, it is crucial to prioritize securing your Linux server from potential cyber attacks. By implementing regular software updates, using strong passwords, setting up a firewall, and disabling unnecessary services, you can significantly decrease the risk of a successful cyber attack. Additionally, regularly monitoring your server for any suspicious activity and investing in intrusion detection systems can help you to proactively defend against potential threats. Remember, the security of your Linux server is ultimately in your hands, so taking these proactive measures is essential to protect your data and system integrity.
FAQ
Q: What are the essential steps to secure my Linux server from potential cyber attacks?
A: The essential steps to secure your Linux server from potential cyber attacks include keeping your system updated with the latest security patches, using strong authentication methods, configuring a firewall, disabling unnecessary services, and implementing intrusion detection systems. It is also important to regularly monitor logs and conduct security audits to identify and address any vulnerabilities.
Q: What are some best practices for securing SSH access to my Linux server?
A: To secure SSH access to your Linux server, you should disable root logins, use key-based authentication instead of password authentication, and change the default port for SSH. Additionally, you can implement tools like fail2ban to automatically block IP addresses that show malicious behavior, and limit the number of login attempts to prevent brute-force attacks.
Q: How can I protect my Linux server from malware and viruses?
A: To protect your Linux server from malware and viruses, it is important to install antivirus software specifically designed for Linux systems and regularly scan for malware. Additionally, you should be cautious when downloading and installing software from untrusted sources, and implement file integrity monitoring to detect any unauthorized changes to system files. Keeping your system updated with the latest security patches and conducting regular security audits will also help in preventing malware and virus infections.













